Gartner highlights the criticality of document-centric real world identity proofing and the handling of Personal Information for all Identity, Access Management and Fraud Detection activities.
Following its recent Market Guide for Identity Proofing and Affirmation 2022, Gartner has now released its Buyers Guide for Identity Proofing 2022 to assist understanding and procurement of Identity Access Management and Fraud Prevention products and identity proofing services. The guide cites 5 findings and 4 recommendations for those seeking to procure products, and Inverid are pleased to see many fundamentals often missed during procurement highlighted in the market guide.
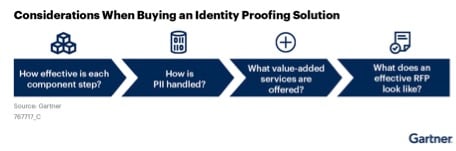
Four steps in identity proofing - Gartner Buyers Guide for Identity Proofing 2022.
Included in the key findings of the guide is that “insufficient depth of understanding of the core building blocks of the identity proofing process” was common. 3 out of Gartner's 4 recommendations are therefore geared towards understanding and thus requesting, assessing and procuring the core building blocks of identity proofing and verification to ensure best of breed vendor(s) selection.
Near Field Communication (NFC), or in common parlance identity document ‘chip reading’ of ICAO 9303-compliant documents, is one of the core building blocks for a true digital experience, bonding the government affirmed or issued document identity ecosystem with the digital identity ecosystem securely and satisfyingly.
(NFC) is considered the highest-assurance method of assessing a document.
We have long advocated that for both security and customer experience that the benefits of an NFC First approach have often been overlooked. More importantly, where they have been realised, a significant competitive advantage has been achieved with the highest conversion rates. Gartner recognises that NFC “is considered the highest-assurance method of assessing a document” in regards to digital proof of identity.
This statement, however, only holds true when the security mechanisms within the chip are utilised to their fullest potential. Document authenticity checks and clone detection must be carried out via an architecture that maintains the inherent high security standards of the ICAO 9303 specification. As with all security, the weakest link becomes the most natural attack vector for those wishing to exploit solutions. Where shortcuts are taken with the identity document checks (e.g., not utilising all the checks in a secure manner), the fundamental basis for bonding a digital identity is flawed and therefore vulnerable right from the start.
For those wanting to learn more about the technology behind NFC, we recommend our Tech Session on NFC.
Handling Personally Identifiable Information
The Gartner buyers guide also highlights in its findings that “Vendors vary greatly in how they handle and store [Personally Identifiable Information PII]” with a recommendation for “interrogating vendors on their approaches to managing PII — paying particular attention to deployment models, automation levels and value-added features information (PII) and their reasons for doing so”. At ReadID, the secure handling of personal data is the highest priority.
Gartner recommends "interrogating vendors on their approaches to managing PII". ReadID does not retain personal identifiable information.
Inverid have always been transparent in their handling of PII data. Our customers have total control of all PII retention periods. Inverid will never store PII beyond that required for the identity proofing session, and as we offer a fully automated solution no human ever sees the PII. Anonymous transaction meta data with no relation to the individual is retained to measure and actively improve the overall product and service; a critical element to manage impact when new mobile devices and eDocuments come to the market.
Privacy is paramount at Inverid
We take information security extremely seriously, and as such Inverid is externally validated on our security and privacy by independent third-party auditors. As such, we have been certified against EU regulation eIDAS 910/2014 to the highest 'Qualified' status. In addition, we have extended or ISO/IEC 27001 Information Security Management certification with the ISO/IEC 27701 Privacy Management certification, furthering our commitment to managing security and privacy of personal information. Our ReadID product is also certified under the American Institute of Certified Public Accountants (AICPA) SOC2 Type2 gold standard for data security.
For those wanting to learn more about secure protection of personal information through certification, we recommend our Tech Session on trust levels.
Conclusion
We recognise and endorse Gartner’s Tool: Questionnaire Template for Identity Proofing RFP which will assist many organisations to procure strong solutions for their requirements – especially in the dark arts arena of optical identity document verification, where evaluation standards are not available yet. Historic reliance on the unvalidated optical verification arena can and is being reduced through the highly secure NFC First approach.